TeleTrace
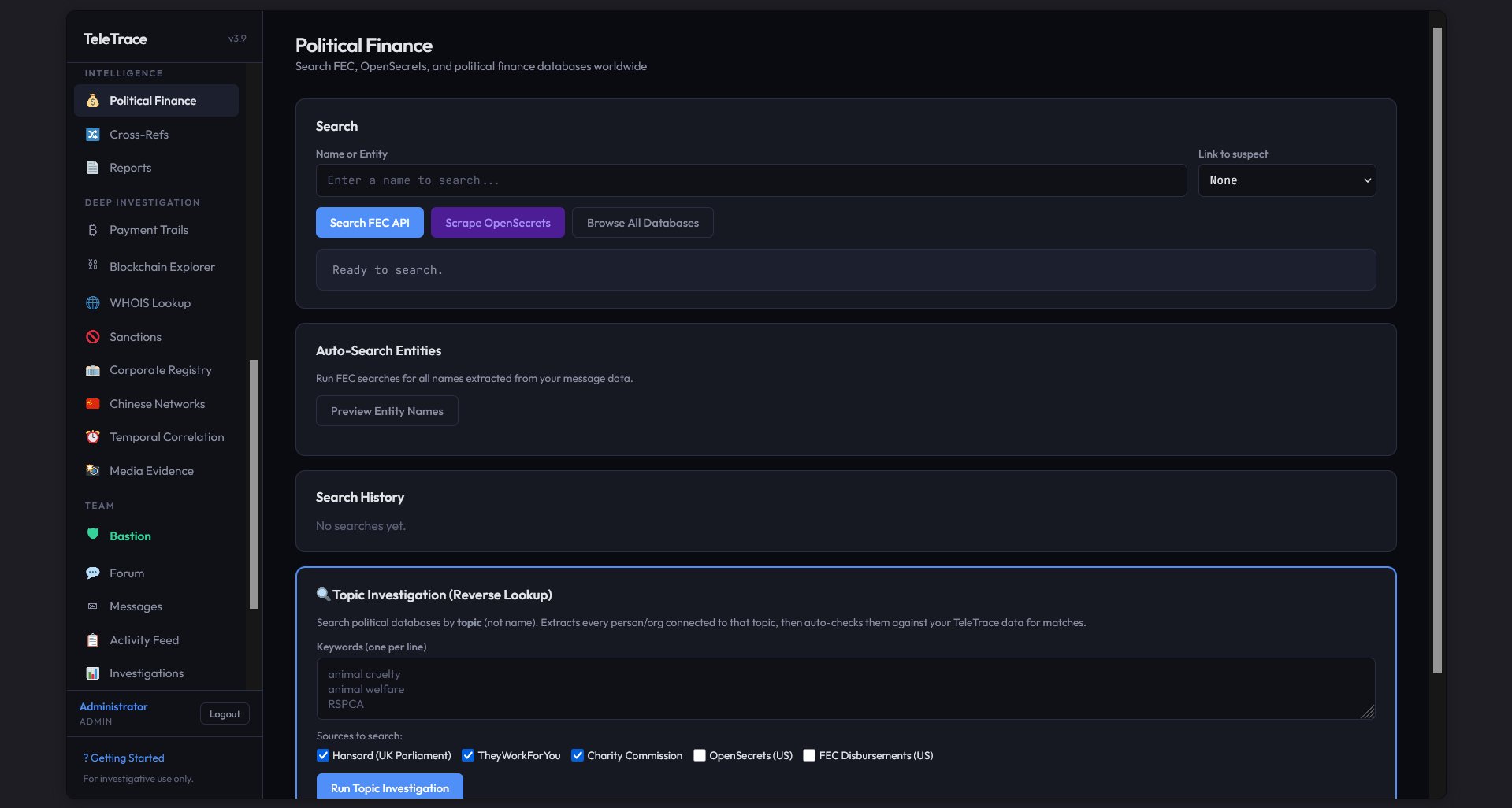
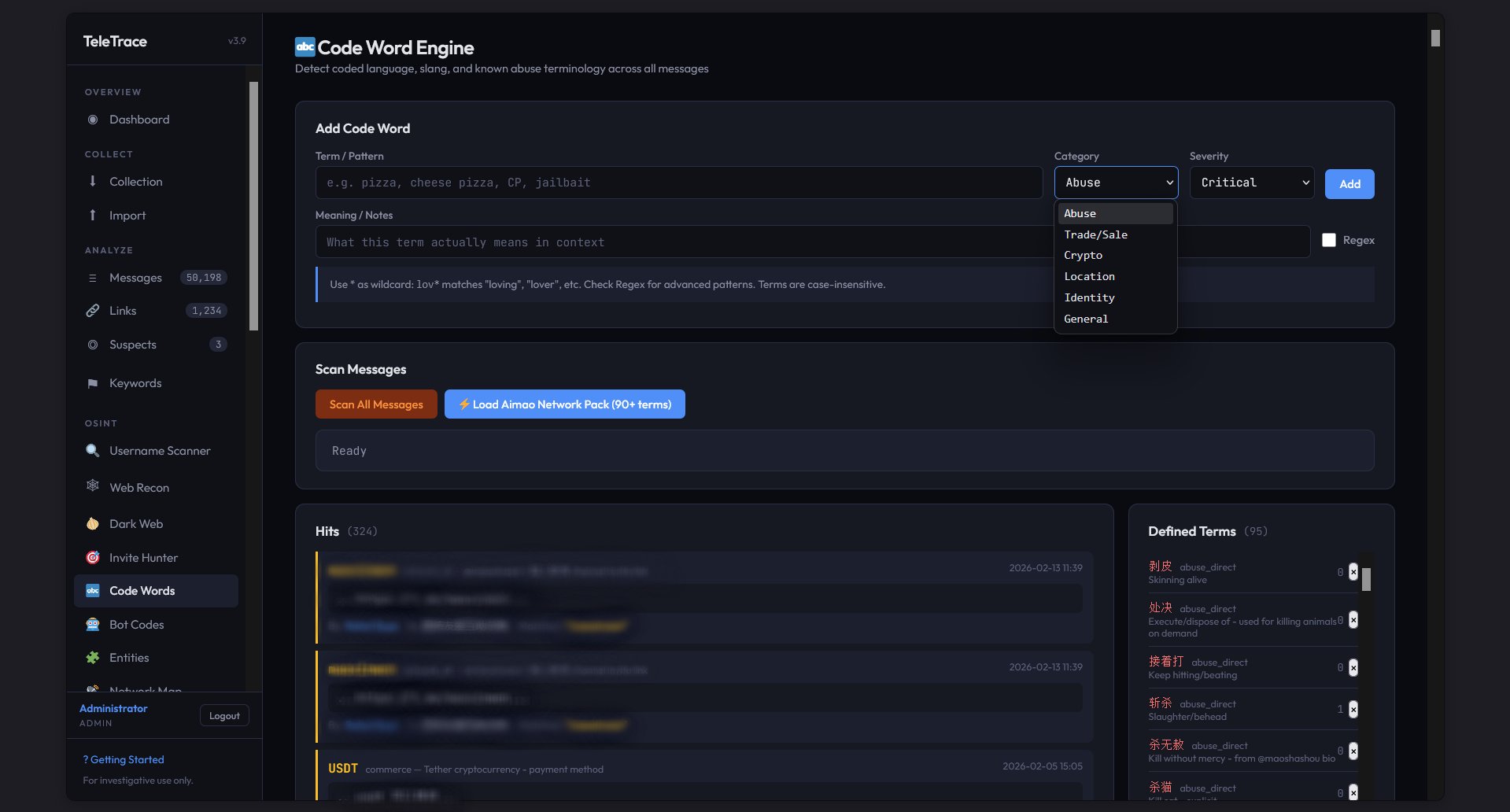
Telegram evidence collection and multi-platform OSINT suite. Collect messages, map networks, track coded language, trace financial connections, and build airtight evidence packages for investigations that matter.
"Built for those who refuse to look the other way."
Overview
TeleTrace is a full-stack investigative platform built to collect, analyze, and preserve evidence from Telegram and beyond. It started as a Telegram scraper and grew into a multi-platform OSINT suite with 30+ modules spanning collection, analysis, deep investigation, and team collaboration.
It runs as a Tor hidden service, accessible only through Tor Browser. No clearnet exposure, no third-party cloud services, no tracking. All data lives on a secured server. Evidence packages include SHA-256 integrity hashes for chain of custody.
Access is invite-only. If your work involves investigating abuse networks, tracking bad actors on Telegram, or building evidence for law enforcement referrals, reach out.
Collection
Full message history, sender IDs, replies, forwards, and metadata. Requires a burner Telegram account. Built-in rate limiting and account rotation guidance to minimize detection.
No login required, no ban risk. Scrapes public channels through the web preview. Limited history depth, channels only. Safe for passive reconnaissance.
Import from Discord (DiscordChatExporter JSON), Reddit (JSON), or generic CSV/JSON. All messages merge into a unified database for cross-platform analysis.
Analysis & OSINT
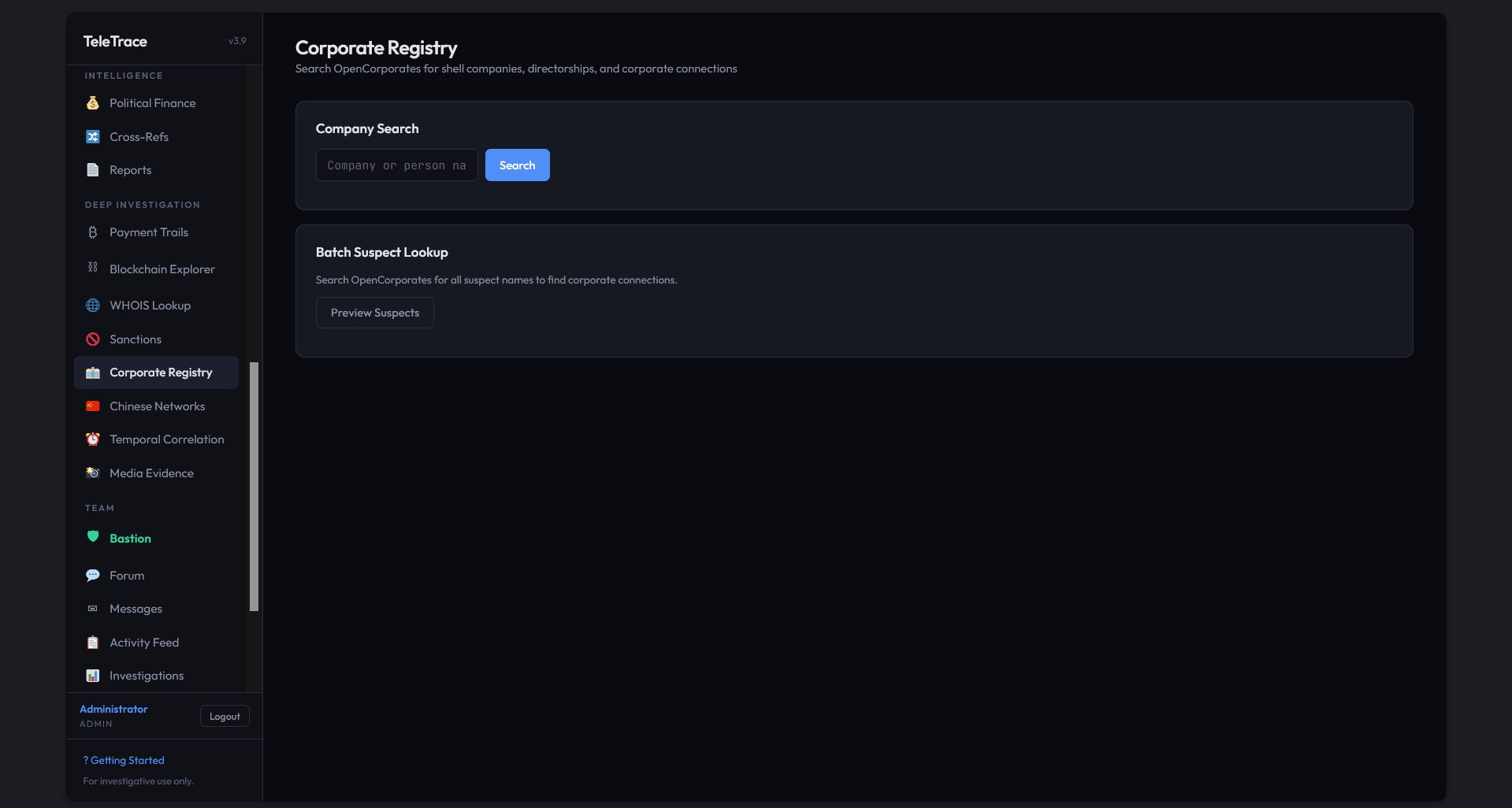
Deep Investigation
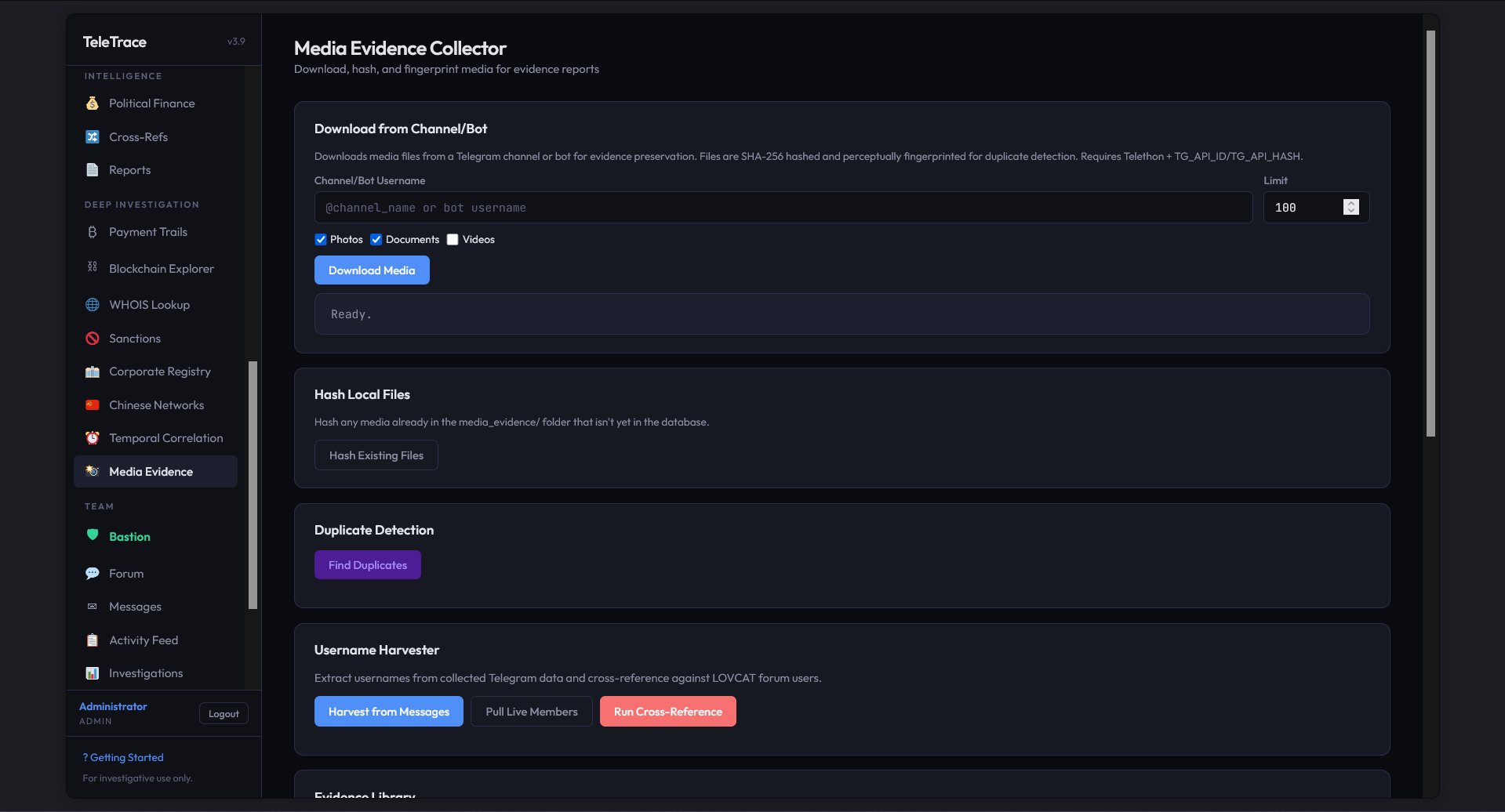
Team & Evidence
TeleTrace supports multi-user collaboration through its Team system. Bastion acts as the team hub. Members can coordinate through an internal forum and messaging system, share investigation notes, and track progress through an activity feed. The Investigations module lets teams organize evidence around specific cases.
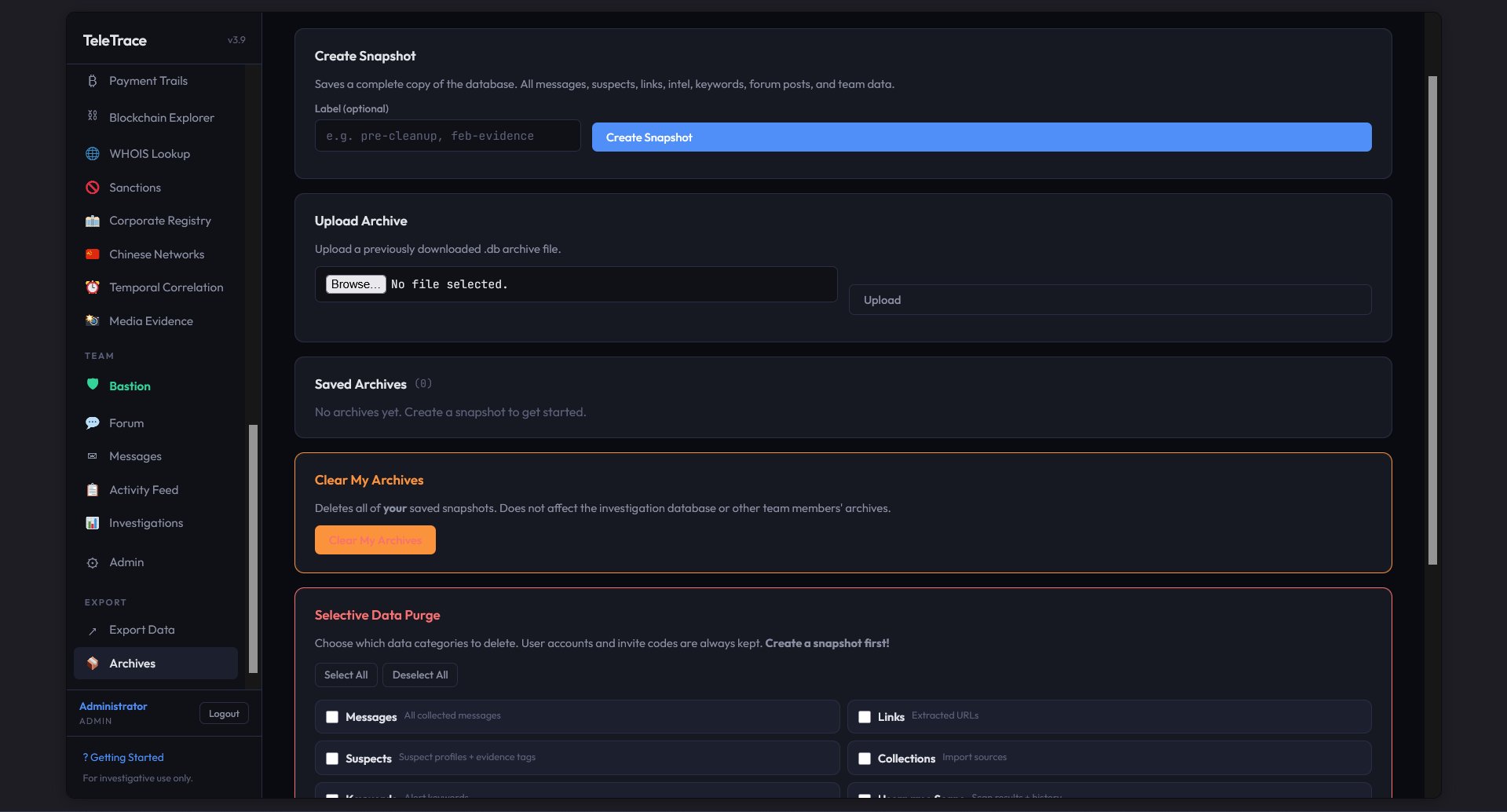
All evidence is tamper-evident. Database snapshots can be created, labeled, and archived for preservation. Selective data purges let you clean categories without losing critical records. Evidence integrity is non-negotiable.
Screenshots
Screenshots contain blurred regions to protect active investigation data, suspect identities, and ongoing case information.